Hackers at the Front Door?
Most every home and business office now has a firewall that separates your internal computer network from the wild west of the world wide internet. The good news is that firewalls have become increasingly more sophisticated and properly configured can do an excellent job in securing your internal computer network devices. Modern firewalls now include intrusion detection and prevention, email spam filtering, website blocking and most are able to generate reports on who did what and when. They not only block evil doers from outside your network, but they police the users on the inside from accessing inappropriate resources on the outside internet. Employees can be blocked from visiting sites that can rob your business of valuable productivity time or violate some security compliance requirement. Prime business hours is really not the time to update your Facebook page! Nor do we want our medical and financial service folks using an instant messaging service to chat with and outsider!
The Firewall is the electronic equivalent of the “front door” to your computer network and there is an endless parade of potential evil doers spray painting your doors and windows, relentlessly looking for a way in. A properly configured, managed, and regularly updated Firewall can be very effective in protecting your computer network, both in the office and at home. Behind the firewall, must desktop computers and office servers have local software based firewalls installed that also provide virus protection. Hopefully if something does get past the firewall, the internal virus and desktop firewall solutions will provide an additional level of security.
What is a Firewall Anyway?
Firewalls are both reasonable and appropriate but here is the bad news. Most of the hacking you now hear and read about is not done by evil doers coming through your firewall! The real damage is done by those inside your network! Malicious users and dishonest employees will always a treat. There is always the treat of the unscrupulous employee swiping credit card data or passing security information for money. The real danger, however, is from users who are just ignorant of today highly sophisticated security vulnerabilities. The most honest employee can unwittingly become the source of a major security breach resulting in the loss of their own personnel data, or the personal and financial data of your customers.
Take your average laptop user as a perfect example. How many times have you gone down to Starbucks and setup shop? Beautiful day, open air, sun and a high speed internet connection, wireless phone and it is business as usual! If I told you how easy it is to setup a “man in the middle” attack at Starbucks you would give up coffee for the rest of your life. You think you are on the Starbucks WiFi, but actually that kid in the back of the Starbucks with the Wireless Access Point attached to his USB connector, has spoofed you into thinking he is your door to the Internet. He has been monitoring every key stroke on you laptop since you logged in. In fact he now has your log in, password and most everything else on your computer. Now when you head back to the office and plug in, you just unleashed a bot on the company network and he will be back later tonight!
If laptops were not enough, everybody is now walking around with a Smartphone! Did you know that your Smartphone keeps a list of all the WiFi networks you have used recently? Remember when you were down at Starbucks checking your email while waiting for that cup of coffee? Now everywhere you go your phone is sending out a beacon request that sounds like “Starbucks WiFi are you there?” hoping it will get a response and auto connect you to the internet. Remember that kid we were just talking about? He decided to answer your beacon request with a “yeah here I am, hop on!” Just another “MITM” attack and what he can do to your Smartphone, especially those Androids makes your laptop look like Fort Knocks!
Sometimes for fun and entertainment, while sitting at a gate in an airport waiting room, I will net scan the WiFi to identify how many phones, computers and ipads are online and connected. Not saying that I would do this, but I think you could execute a Netbios attack in less the five minutes? It is amazing how many people leave their printer an network sharing options on when they travel. Even more people leave their “Network Neighborhood” settings in the default configuration! The drill is always the same: map the network to see what hosts are connected; port scan for know vulnerabilities; out the exploit tool kit and the rest is actually getting relatively boring for the ethical hacker. Now credit card thieves on the other hand…….
Chances are your Internet browser is worst enemy when it comes to securing your privacy. Every website you visit, every email you send and every link you follow is being tracked by hundreds of companies. Don’t believe me? If you are using Firefox, install an add in extension named DoNotTrackme and study what happens. Assuming you are an average internet surfer, in less that 72 hours you will have a list of over 100 companies that have been tracking your every move on the internet! These companies don’t work for the NSA, but they do sell your “digital profile” to those willing to pay for the information. Where has your GPS been? What sites did you visit, what movies did you watch, what products did you buy, what search terms did you select – all of this dutifully reported back by you and your unsuspecting employees. Ever wonder if your competitors want to know what your viewing on line?
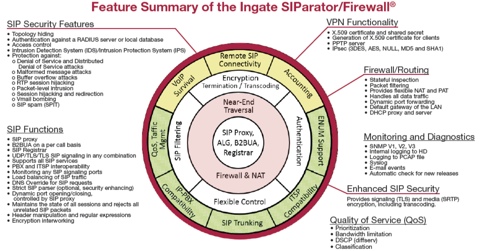
Voice Over IP phone systems offer an entirely new range of vulnerabilities waiting to be exploited by the unscrupulous evil doer! We recently illustrated to a client Law Firm (as a paid intrusion detection and penetration testing consultant and with the clients permission) just how easy it is to covertly switch on a conference room based speakerphone and broadcast the entire conference to a remote observer over the internet! In fact, capturing voice packets for replay is the first trick script kiddies learn in hacking school!
VoIP, Bluetooth, WiFi, GPS, RFid, file and print sharing and even the “cloud” all add up to a list of vulnerabilities that can be easily exploited. What can you do? You need to educate yourself and develop your own “best practice” for safe computing. You need to educate your employees and co-workers about the various vulnerabilities we all face every day as we become more “wired” and more Mobile. Hire a competent Computer Network Security professional to do “penetration testing” on your corporate network and firewall. It would be better to pay a professional to “hack” you, then pay to fix it after you have been hacked! Remember if we can touch your network, we will own your network!
(DrVoIP provides VoIP network readiness assessments and is a certified Network Security consultancy. If you contact DrVoIP@DrVoIP.com we recommend that you use Ipredator to do so!)