ShoreTel ECC Future?
The ShoreTel ECC or enterprise contact center is a remarkable product in many ways. Though we are depressed to see that it has apparently taken a back seat to ShoreTel Connect as it relates to product enhancements, it remains a formidable player in the contact center space. Clearly, if you are deploying a ShoreTel phone system, then it may be the only viable option. We note that ShoreTel has made a new acquisition for contact center functionality in the cloud, so the potential of supporting ECC product enhancements may even be less hopeful as product development resources shift to the “cloud” and ShoreTel Connect.
Remember EasyRun?
We have worked with the ECC since before it was a ShoreTel product. It actually originated as an OEM product, a re-branding of a software solution brought to market by EasyRun, an Israeli based company founded by Avi Silber, long time VP of Software Development for Telrad. ShoreTel ultimately executed a software source code licnese and the rest is history. Unfortunately, we seem stalled at Version 9 of ECC, which was not a major evolutionary step from ECC Version 8.
At any rate, the product does a super job in small to medium sized Call Centers and meets the minimum daily adult requirement for call center functionality. One particular function enables the system to integrate with popular database solutions like Microsoft SQL. This enables the system to take on some very sophisticated applications that include routing inbound calls based on the return of data in the customer service database. One of them most asked questions of marketing professionals as it relates to Contact Centers: “are all customers created equal”. You might want to route an incoming call based on the callers status in your customer database as a Platinum client or as a deadbeat on credit hold.
SQL database dips are almost essential for any Contact Center offering. ShoreTel enables this functionality through OBDC connectors to the host SQL server or CRM system. One of the challenges for design and implementation engineers is testing the design and results of the SQL data dip. Historically, ShoreTel has not provided a lot of debug tools here and documentation on inner workings of the ECC is not generally available. If you are bold and go poking around in the BIN files, you will note a lot of exe files and if you are curious, brave and inquisitive you might take on an exploration of what these files are used for.
Undocumented ShoreTel Debuggers!
One file in particular seems to launch a very useful test tool. We have never found any documentation on it, and it has become something of a legend among we ECC implementation engineers. If you are fortunate enough to maintain a relationship with other engineers that share information, you can build up a library of useful tools based on shared results from others. Kudu’s to one such brilliant engineer, Bill Fraedrich for sharing his growing list of FC_Thingy functions and the other members of the development community who regularly publish results.
Route Caller by ANI (caller ID)?
Recently we had to create a SQL data dip to pull back a customer record using Caller ID or ANI as the database index. Now anybody who has done any Contact Center CRM integration regardless of vendor, knows that you have to do some string manipulations to strip off the +1 that will be passed by the carrier as part of the ANI information. ShoreTel ECC, CISCO UCCX, it does not matter it is all relatively the same. Once you clean up the ANI you can pass it off as part of a SELECT command and go get your data. Then manipulate the data to find the fields you are looking for to make your routing determination.
The undocumented debugger!
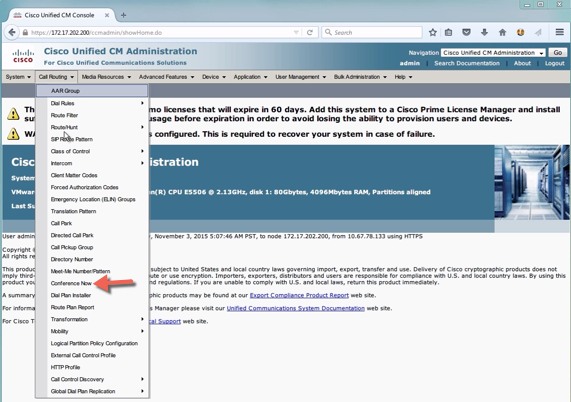
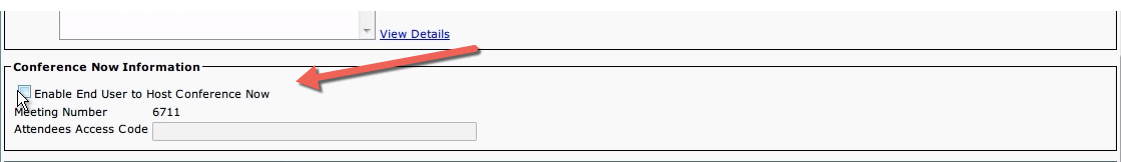
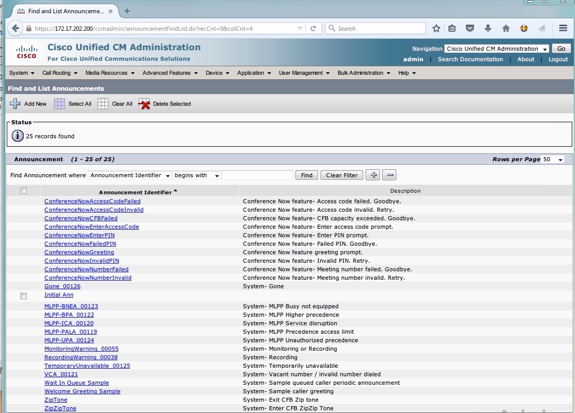
The issue becomes how do debug a script that is not producing the results your design expected? Again, ShoreTel comes up short here as it relates to documented debug tools. The CISCO UCCX, for example, has a step by step debugger built right into the script editor, which is really helpful for those of us who have to design, implement and test these scripts. It turns out that ShoreTel has one as well, you just have to know where to find it. Again it is not documented and is well known only to those that know it well.
In this video clip we take a look at the tool and show an example of how you might use it to unravel a particular SQL data dip problem. We have found a number of these tools and we are always looking for documentation and road maps produced by those who have gone this way before! Next blog we will take a look at a TAPI debugger that is also very useful when troubleshooting ShoreTel phone system Communicator issues.
At any rate, the ShoreTel ECC has great potential and is a wonderful solution when applied in the proper environment. You can create some very sophisticated routing applications based on a variety of CRM integration, custom software solutions and IVR scripts. Despite all our grumbling and complaining, we have not found anything we cant make work on a ShoreTel ECC!